Phineas Fisher, Hacktivism, and Magic Tricks
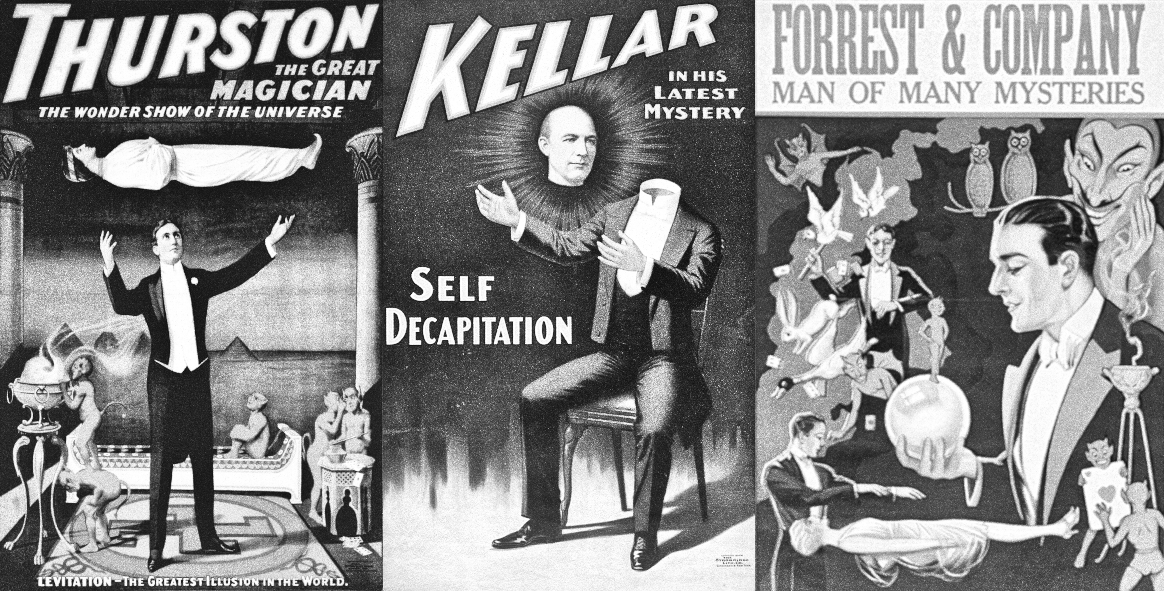
It's said that a good magician never reveals their secrets. Computer hacking is a particularly good type of magic trick, and for the most part, hackers don't reveal their secrets either. It's sometimes hard to reconcile this, because we read about hacking all the time -- in newspapers, at conferences, in blog posts, on social media -- but mostly we only think we're reading about hacking. There's a subtle difference between learning the mechanical hand movements needed to stack a deck of cards, and performing a magic trick in front of a crowd.
Occasionally though, a hacker breaks the mold, and you get to see how the magic works up close.
In 2014, Phineas Fisher started tweeting from a parody Twitter account of Gamma International, the company responsible for the FinFisher/FinSpy surveillance software. Phineas Fisher had hacked the company and was in the process of leaking customer lists, price lists, support documentation, and source code. A classic "hack-and-leak" operation.
A company having their intellectual property leaked online isn't unusual though, and financially motivated hackers use the threat of leaks in a standard playbook called "double extortion ransomware". Two things made the Gamma International hack stand out however:
1) There wasn't a clear financial motivation, and although there's some debate, Phineas Fisher didn't appear to have clear connections to state-sponsored hacking either (see Chapter 11 in Joseph Menn's book on the Cult of the Dead Cow for an alternative take). Phineas Fisher claimed to be hacking for political and ideological reasons, e.g. they claimed to be an activist.
2) A few months after the Gamma International hack, Phineas Fisher released an "e-zine" style document called "HackBack: A DIY Guide for those without the patience to wait for whistleblowers" that outlined their end-to-end hacking methodology. The magician had revealed their secrets.
It didn't stop there. In 2015, Phineas Fisher performed a similar hack-and-leak operation on Hacking Team, followed by a similar e-zine called "HackBack: A DIY Guide". After a 2016 hack of the police union of Catalonia, they released a 40 minute livestream video of the hack. After a 2019 hack of a bank in the Cayman Islands, they released "Hack Back: A DIY guide to robbing banks". In releasing the HackBack series, Phineas Fisher hoped to inspire a movement of hackers participating in a style of activism known as direct action.
Gabriella Coleman likes to call this "public interest hacking". It's rare to see this specific intersection between technology and politics. You need to know how to hack, and you need to know what you're hacking for. Most hacking is done for financial advantage, and a lot is done for geopolitical advancement, but it's actually quite rare that hacking is done in the name of social change.
It's also rare to get a detailed behind the scenes look into the tactics and technique used in this kind of operation. In this post I wanted to take a closer look at the technical contents of the "HackBack" series, and to consider whether this style of hacking is still relevant today.
HackBack 1 ("A DIY Guide for those without the patience to wait for whistleblowers" -- 2014):
- The first consideration is operational security. They recommend using Whonix + Truecrypt (you'd probably use Veracrypt hidden volumes today), but they note that hacking over the Tor network can be logistically painful (or impossible) because of the network latency, and the need to route traffic for a reverse shell. This means they maintain several hacked or rented servers that they then access over Tor. This advice appears pretty consistently throughout the series -- Phineas Fisher felt that this setup, if used correctly, would be sufficient to protect their identity.
- The initial process is a standard pentesting enumeration. Given a target and its known domain names, bruteforce the subdomains and then use whois to record any related IP address space (privately owned IP blocks vs cloud-owned stuff). Try to resolve everything in those ranges, and repeat. Google search for IP address space that matches the customer name/address. Then once you have a list of hosts, port scan everything.
- From there they're first looking for anything that looks like it shouldn't be there, like a file service or web application that's unauthenticated. Looking for common misconfigurations like default passwords on known services. And looking for stuff with known vulnerabilities that are unpatched.
- For web applications, they start by browsing around and familiarizing with each environment. Then they run WhatWeb to get a sense for what software the endpoint is running, and Nikto to look for any low-hanging fruit.
- Otherwise they try to find a new vulnerability.
- For custom applications, that usually means using a web intercepting proxy (they use ZAP) and doing a mix of manual and automated testing. In particular, they seem to be a big fan of using sqlmap to explore potential SQL injection attacks.
- For third-party applications, they try to buy or steal a copy of the software and poke around for bugs in an offline environment.
- Once they have a shell (they seem to regularly find ways to drop a PHP shell), they say that around 50% of the time you'll be able to get root by exploiting known vulnerabilities or misconfiguration (like a www-data writable cron script that runs as root).
- From there, they suggest pivoting around the internal network using a process similar to that described in the first bullet point.
HackBack 2 ("A DIY Guide" -- originally written in Spanish -- 2015):
- Some additional operational security advice: don't reuse any infrastructure (e.g. servers or proxies) between hacks, tear it all down and start from scratch for each project.
- They talk about their options for initial entry on the Hacking Team network. There wasn't a huge external footprint, but they decided to target a commercial network appliance that they were using. They managed to find a remote root exploit (later this turned out to be a SonicWall device that was vulnerable to shellshock).
- Before launching the attack, they had everything prepared. They had tested the exploit, wrote a rootkit/backdoor for the target device, and had post-exploitation tools ready to go.
- From there they tried to pivot. First they found an unauthenticated MongoDB instance, but it didn't contain much of interest. Then they found a Synology iSCSI device that was exposed to the corporate network due to a network configuration error. This device was used for backups.
- From this they found a backup of an Exchange VM, and from this they found the password for a local admin that still worked on the live machine. They could use this account to get domain admin (essentially by using mimikatz). With domain admin they can dump the mailspool and other sensitive files.
- There's a detailed discussion on lateral movement in a Windows network, using all the common favorites like PSExec, WMI, and group policy. They used the group policy technique to compromise an admin and get access to their development network. They also note that advanced persistence techniques are overrated for their style of hacking, but they do try to keep multiple options for reentry alive (like backdoors and dumping legitimate credentials).
- They note that everything they're doing here is forensically noisy in pretty common/expected ways (like event logs that usually correspond to malicious behavior), but that most of the time nobody is watching closely enough to notice, at least not in time. Eventually they stole Hacking Team's Twitter password by using the password reset feature.
HackBack 3 (40 minute video "Hacking Sindicat de Mossos d'Esquadra" -- 2016):
- They find a SQL injection bug and then use sqlmap to get an arbitrary file read. Using this they dump the PHP scripts for the target application. From there they find a standard PHP file upload vulnerability, but it's in a script that requires admin access. They use the SQL injection to dump the unsalted hash for the admin's password, which they then crack.
- Using the PHP shell they dump the local MySQL database using creds they found in the source code, and they steal /var/www/. Then they backdoor all of the login pages ("Don't crack hashes, backdoor login pages. It's better for the environment."). One of the passwords stolen this way was reused for their Twitter account.
HackBack 4 ("A DIY guide to robbing banks" -- originally written in Spanish -- 2019):
- They talk about taking the output of one of their previous hacks (e.g. the SonicWall exploit) and scanning the Internet using zmap/zgrab to find other hosts that are affected. It's still possible to find interesting targets using a more opportunistic approach like this (as opposed to finding specific vulnerabilities intended for a specific target).
- Then they wrote a login page backdoor for the VPN appliance, and a lot of those passwords also worked for the internal Windows network, including a domain admin.
- Keylogging and regularly timed screenshots allowed them to narrow in on employees that had access to the SWIFT network, and then studied those employees to see how transactions are approved.
- They talk about how in their opinion the age of offensive PowerShell is about to be over because of the introduction of the Antimalware Scan Interface (AMSI) hooks for PowerShell (e.g. the risk of detection using these techniques is getting too high).
- Finally, they say "the two most important skills by far for practical hacking, are phishing and social engineering for initial access, and then being able to escalate and move around in windows domains".
And that's all... for now, at least.
My first reaction is that it's all remarkably unremarkable. If you've worked professionally as a pentester before, nothing in this list of techniques is likely to surprise you. Without a doubt, understanding how a magic trick works destroys the mystery.
My second reaction though is that there's still something beautiful about any style of hacking that can be performed by a single person and that doesn't involve tricking people with phishing or malware. Phishing and malware works just fine -- in fact you can see Phineas Fisher trending in that direction in his own approach to initial access -- but it just has a level of inelegance that makes it harder to appreciate. Phishing is the magic trick that makes the watcher feel foolish instead of amazed. There's no mystery at all.
Most hacking is done by teams these days, and that's fine. Some teams are incredibly structured and process-driven, and some teams are just based on ad-hoc arrangements like splitting up initial access and ransomware operations into different verticals. Maybe the attraction of solo hacking is just the purity of the accomplishments that result. It's hard to see the "craft" in hacking when your only job is to press a magical hacking button that someone else has built for you, and it's hard to see the craft if you're a 1/16th part of making that button.
In any case, Phineas Fisher successfully made the point that with a small amount of technical know-how and a lot of time, motivation, and persistence, you can have a real impact on the world around you, albeit by committing crimes. I'd argue that Phineas Fisher's actions had an indirect role in the frantic discussions around using the Wassenaar Arrangement to control the export of intrusion software, the many public controversies of the embattled NSO group, and the US Commerce department using the Entity List to restrict trade with spyware companies.
For what it's worth, Phineas Fisher's take on regulations for spyware: "I don't really care so much about that kind of stuff though. Intel agencies and police do what they want regardless of regulations, and criminals like me do what we want regardless of regulations. I guess it just provides a way for professional activists to feel like they're accomplishing something". Fair enough.
It's a subtle balance though. When a spyware company is denounced for providing these kinds of capabilities, someone out there is inevitably thinking "our enemies have these tools, and we should too" rather than "this is horrible and we should stop it". So a one-off hack might not do much, you really need to build a campaign around your message -- or you need to build a movement.
This is what Phineas Fisher was trying to achieve with the HackBack series. "I don't want to be the lone hacker fighting the system. I want to inspire others to take similar action, and try to provide the information so they can learn how".
It's hard to build a movement though, and arguably the HackBack series didn't entirely achieve its stated goals. There's certainly been some related activity, and a group called Guacamaya has had significant success recently, but it's not exactly a landslide of activity... or an anarchist revolution. The missing ingredient seems to be on the side of motivation, politics, and a willingness to commit crimes, rather than access to good technical information. Still, it was good information.
Are the techniques that Phineas Fisher described still relevant today? With some adjustments, yes. The high-level methodology of reconnaissance and custom targeted bug hunting is still effective, but it's getting much harder to find issues like SQL injection or PHP file upload bugs that Phineas Fisher often used. So the methodology applies, but the specific bug classes might be different. There still seems to be a good amount of command injection, deserialization, SSRF, and file handling issues out there -- but on average they're less obvious and less common than they used to be, so the time investment is likely to be higher.
Enterprise trends toward tool, vendor, and service consolidation means that it can take longer to find the weird stuff as well, and the weird stuff is more likely to be hosted in a cloud environment that has limited opportunities for pivoting toward internal networks. Increasingly you're competing with the bug bounty crowd for the "easy-to-use, critical impact" issues that you need, and increasingly you're running up against EDR systems that make lateral movement and privilege escalation a bit more risky.
Still, with patience and persistence, it's possible to find interesting attack vectors on interesting systems. The probability of success is lower than it was 10 or 20 years ago, and that means that the number of failures you have to wade through to get to the interesting stuff is considerably higher. I suspect it can be hard to maintain the required level of motivation -- hacking is more like 99% grind and 1% magic.
There's an exception to the rule that "magician never reveals their secrets", and it's an exception that I suspect that Phineas Fisher knew well -- while the audience doesn't actually want to know how a trick works, other magicians do. If you teach another magician your tricks, they'll be able to fully appreciate what you're doing, and may even learn a trick or two themselves.
